What is it TRIOFOX?
Triofox is a software platform that enables secure remote file access, collaboration and file-sharing without requiring a traditional VPN setup
Organisations that have large file servers, CAD files, large media or engineering files, and need remote access without the latency or complexity of VPNs. Triofox advertises support specifically for “AutoCAD on Cloud Storage / large photo library over slow VPN”. Teams that want to maintain control of their data (on-premises or hybrid) rather than shift everything into a new SaaS platform. Triofox emphasizes “your storage, your identity providers, Situations where users are spread across branch offices or remote work scenarios and need the experience of a mapped drive, offline access, familiar file-server behaviour rather than a pure web-only interface. Use cases that benefit from smart search of unstructured files: with “Triofox.ai” you can search via natural language to find documents, paragraphs, etc across your file store.
Short Brief Behind the Attack
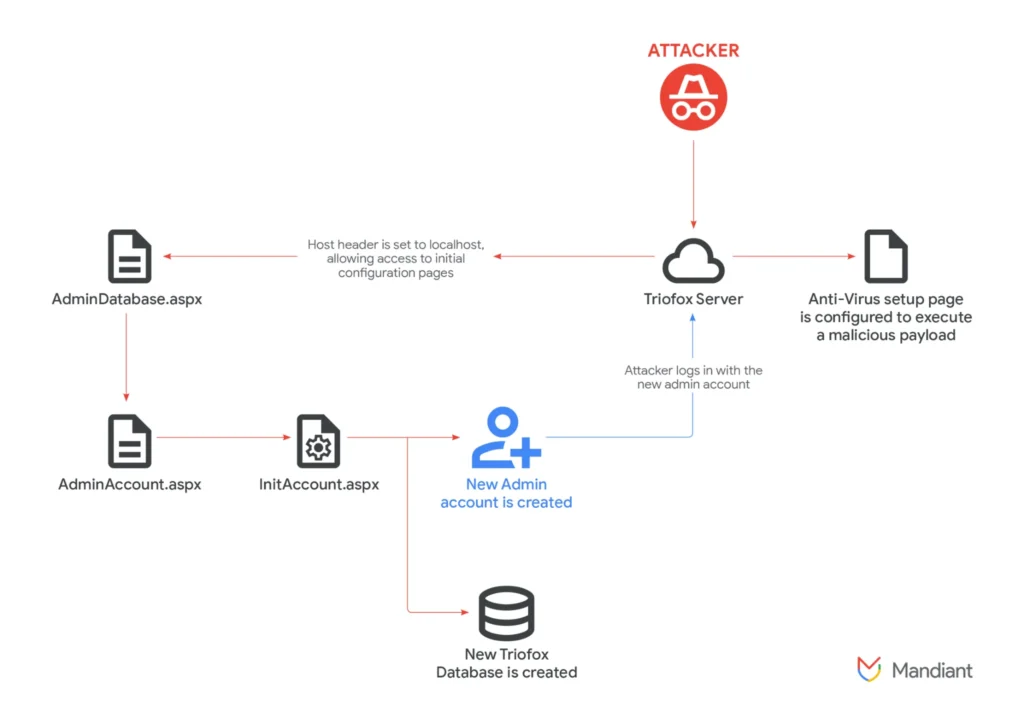
The root cause of CVE-2025-12480 is an access-control logic flaw in Triofox’s web interface. The code governing administrative pages checks whether the request’s HTTP Host header equals “localhost”, and if so it immediately grants access In other words, Triofox trusts the Host header sent by the client. If the optional TrustedHostIp setting is not configured, this host-header check is effectively the only gatekeeper for sensitive setup pages An attacker can exploit this by sending an HTTP request with a forged Host: localhost header. Mandiant observed such a request in the server logs – for example, a GET to AdminAccount.aspx with a referer of http://localhost/… – which would never occur in normal external traffic Under a legitimate context, Triofox would block access (redirecting to AccessDenied), but with the spoofed header the application mistakenly allowed access to pages like AdminDatabase.aspx and AdminAccount.aspx
Attackers exploited a critical vulnerability in Gladinet’s Triofox file-sharing platform to bypass authentication and execute malicious code by abusing the product’s built-in antivirus configuration. The flaw (tracked as CVE-2025-12480) allowed unauthenticated access to administration/configuration pages, letting adversaries create new native admin accounts and change server settings. Once they had administrative control, the attackers pointed Triofox’s antivirus scan path to a remote or staged payload and forced the platform to retrieve and run that file with system-level privileges. This chain produced remote code execution on vulnerable servers, enabling deployment of remote access tools and lateral movement into targeted environments. Security teams observed the activity as early as August 24, 2025, and linked it to a threat cluster tracked as UNC6485; vendors released patches in July 2025 but evidence shows many instances remained unpatched and were subsequently exploited in the wild. The exploit’s high impact stems from Triofox’s role as a gateway to on-premises file servers and identity integrations (Active Directory / SSO), which raised the stakes for organizations that expose Triofox to the internet without compensating controls. Mitigations include applying vendor patches immediately, restricting external access to Triofox management interfaces, enforcing network segmentation and monitoring for anomalous configuration changes, and auditing antivirus paths and file staging directories. Detection guidance focuses on unusual account creations, unexpected writes to staging folders (for example C:\Windows\Temp), and remote access utility usage such as PLINK or unauthorized RDP tunnels. Administrators should also review vendor advisories and implement compensating controls if immediate patching is impossible. This attack underscores how features intended to protect systems—like integrated antivirus scanning—can be repurposed as execution vectors when combined with access-control weaknesses. Organizations using Triofox should also rotate any exposed cryptographic keys, verify integrity of backups, and consider temporary WAF rules, IP allowlisting, and increased logging until full remediation is confirmed.



